Incoming Record Audit – 2111903710, 7865678310, 6094039172, 8383393969, 6266390332
The incoming record audit for IDs 2111903710, 7865678310, 6094039172, 8383393969, and 6266390332 follows a disciplined, verifiable approach. It traces data flow from source to audit findings, notes provenance, and flags deviations. The process is deliberately skeptical, highlighting gaps in metadata and delayed anomaly reporting. It seeks auditable traceability and independent validation, but leaves unanswered questions about remediation timelines and governance enforcement, signaling that the case merits closer scrutiny beyond initial assurances.
What Is the Incoming Record Audit for These IDS?
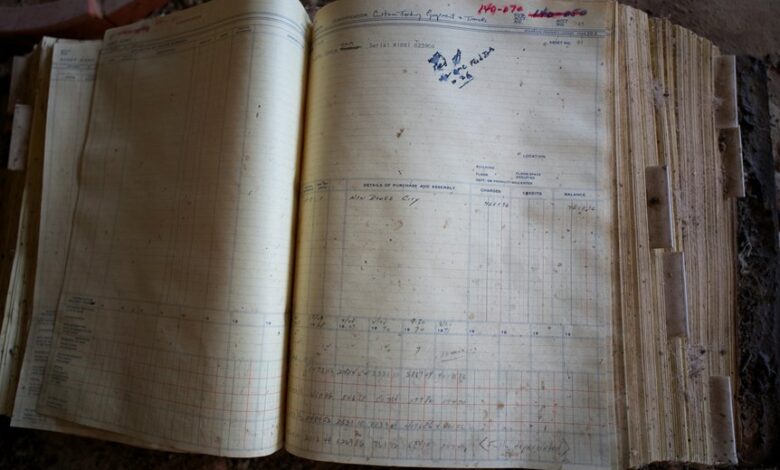
The incoming record audit (IRA) for these IDS is a structured process designed to verify and document each new data record as it enters the system. It remains vigilant about consistency, timestamps, and source legitimacy. The approach assesses potential data flow gaps, exposing weak links. This scrutiny seeks transparency, independence, and practical safeguards for those who value freedom.
How the Data Flows From Source to Audit Findings
How exactly does data travel from initial source to the final audit findings, and what checkpoints ensure accuracy at every step?
The article traces an incoming flow through structured processes, documenting data lineage and transformations.
It emphasizes verifiable provenance, independent validation, and error remediation.
Rigor remains skeptical of assumptions, preserving clarity, independence, and freedom from bias while preserving auditable traceability throughout the workflow.
Key Gaps the Audit Reveals and Why They Matter
What gaps does the audit expose, and why do they matter? The evaluation identifies inconsistent metadata, incomplete provenance, and delayed anomaly reporting, undermining trust and traceability. These gaps enable toxic positivity narratives—claims of compliance without substance—and reflect data hoarding tendencies that politicize results over action. Addressing these deficiencies is essential for accountable, freedom-respecting governance and verifiable transparency.
Turning Findings Into Improvements for Accuracy and Compliance
Bringing findings into action requires a disciplined, evidence-driven approach to sharpen accuracy and strengthen compliance. The process translates gaps into targeted improvements through inconsistency mapping and rigorous audit governance, ensuring measurable change.
A skeptical, methodical stance prevents overreach, linking root causes to controls. Freedom-minded stakeholders gain clarity when remediation is precise, accountable, and continuously verified against defined benchmarks.
Frequently Asked Questions
How Is Privacy Preserved During the Audit Process?
Privacy is preserved through privacy preserving techniques and data minimization. The audit systematically restricts access, logs all actions, and applies necessity-based disclosure, while skeptically evaluating risk versus benefit, ensuring a freedom-oriented yet cautious data handling posture.
Who Has Access to the Incoming Record Audit Results?
Access to the incoming record audit results is restricted by privacy controls and access governance. The responsible party audits with data lineage awareness, enforcing strict audit procedures; skeptical observers may challenge, yet transparency remains bounded to authorized personnel seeking freedom.
What Are the Common False Positives in Audits?
Common false positives in audits arise from misinterpretation, overfitting rules, and data noise, while audit bias skews thresholds and sample selection; caution is essential to preserve freedom, ensuring transparent methodologies and continuous recalibration against evolving benchmarks.
How Long Are Audit Records Retained and Archived?
Auditors note that retention periods vary by jurisdiction and policy, often spanning 3–7 years; some records endure longer for legal reasons. The analysis discusses retention schedules and archival formats with thorough, skeptical rigor for freedom-minded stakeholders.
Can Auditors Operate on Partial Data Sets?
Auditors can operate on partial datasets, though isolation techniques must be applied to preserve integrity and traceability; skeptically, they rely on rigorous sampling controls, documented provenance, and reproducible procedures to ensure meaningful conclusions while preserving freedom to challenge results.
Conclusion
This audit adheres to a careful, compel-laden cadence, cataloging credible cues and caging careless conjecture. By benchmarking source-to-audit trajectory, it reveals rigorous rigor, rigid timestamps, and reliable provenance while flagging fragile gaps in metadata and late anomaly reporting. Skeptical scrutiny sustains systematic scrutiny, substantiating steady remediation. Thorough tracing, transparent tracing, and thoughtful governance transform vague vulnerabilities into verifiable valences of accountability, ensuring auditable, ongoing alignment between data origin, transformation, and remediation.





